Hot Topics
- June 12, 2019 | Psychology Today: Sex Robots And The End Of Civilization
- March 30, 2019 | HB57: Utah Now Requires Search Warrant To Access Electronic Data
- April 19, 2024 | Transhumanism, Digital Twins And Technocratic Takeover Of Bodies
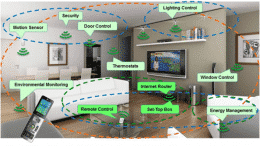
- April 18, 2024 | Skynet Has Arrived: Google Follows Apple, Activates Worldwide Bluetooth LE Mesh Network
- April 17, 2024 | UBI: Red States Fight Urge To Give ‘Basic Income’ Cash To Residents
- April 16, 2024 | Hall Of Shame II: Thanks To Congress, The NSA Is ‘Just Days From Taking Over The Internet’
- April 15, 2024 | Hall Of Shame: Congress Votes For Warrantless Surveillance Of Americans
- April 12, 2024 | Technocracy: “The Science Of Social Engineering” And The End Of Debt