
This author cracks the Technocrat conspiracy to use the FDA to institutionalize Transhumanism. Future testing of drugs and therapies will be conducted on digital twins or directly on humans instead of animals. This is a sea change in health (dis)care, paving the for the endless use of EUA to "approve" new drugs.
Health Systems
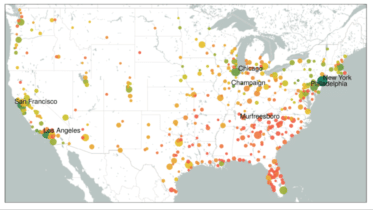
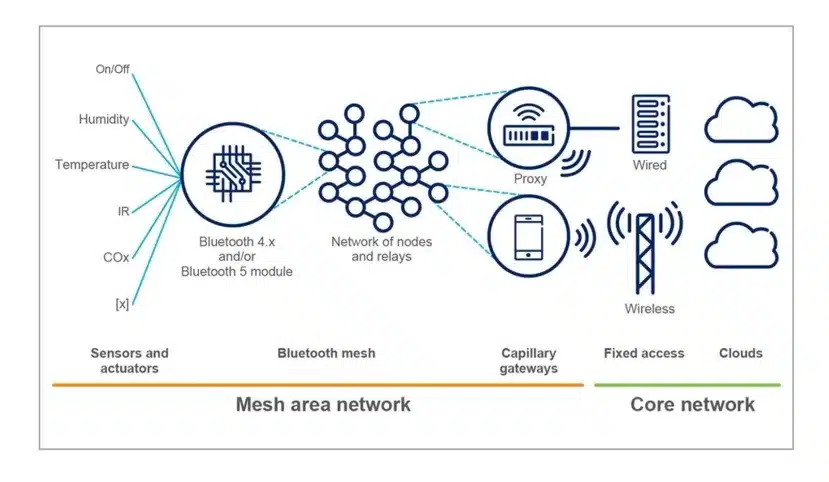
Wearables: Smartphones, fitness trackers, Smartwatches, hearing aids, Apple Air Tags, Ring products, etc., all use Bluetooth LE (low energy) to form an independent "mesh network" that is not based on the Internet. All these devices can receive, send, and forward data packets and instructions to other devices. Almost all IoT devices will be equipped with BLE. Thus, the INFRASTRUCTURE is complete, just waiting to sink its teeth into humanity everywhere.
Total Surveillance Society
The Universal Basic Income (UBI) movement is global, being pushed straight from the top by the United Nations, which exists for Sustainable Development, aka Technocracy. In America, it pushed by the National League of Cities that shepherds over 2,700 of the largest cities. Academic institutions like Stanford University, University of Michigan and Arizona State University are pushing it hard.
Universal Basic Income
Hall Of Shame: Congress Votes For Warrantless Surveillance Of Americans
Technocracy: “The Science Of Social Engineering” And The End Of Debt
Flashback 1992: What The Washington Post Wrote About The Trilateral Commission
Islands That Climate Alarmists Said Would Soon “Disappear” Due To Rising Sea Found To Have Grown In Size
Dropped Without Notice: Insurers Spy On Houses Via Aerial Imagery, Seeking Reasons To Cancel Coverage
Trilateral Commissioner Larry Summers, OpenAI Board Member, Says All Labor Will Be Replaced
Bill Gates & UN Behind “Digital Public Infrastructure” For Global Control
Deadly mRNA Vaccine Trial Test Results In Hogs?
Food Systems, Genetic Engineering
Tennessee Senate Says “No” To mRNA Vaccines In Food
Technocracy, Total Surveillance Society