|
Getting your Trinity Audio player ready... |
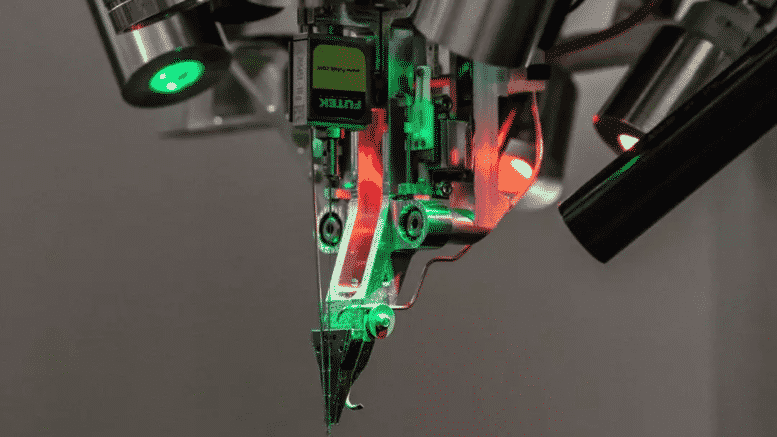
Elon Musk is a consummate Technocrat and Transhumanist who sees the merger of the human condition with advanced technology as the way to achieve Humanity 2.0. Remember that Technocracy is the "Science of Social Engineering."