|
Getting your Trinity Audio player ready... |
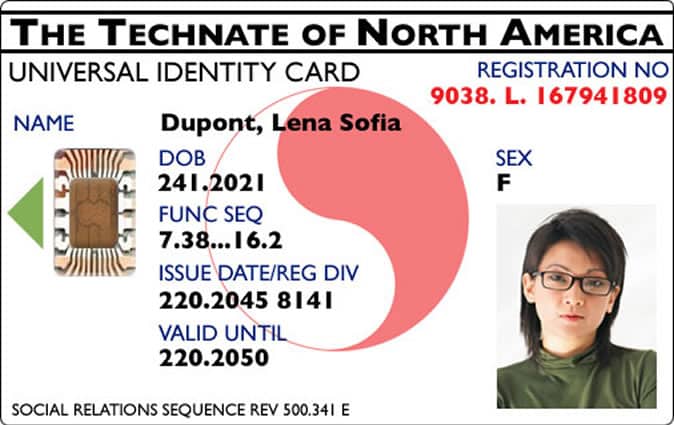
The final solution to implementing Technocracy would be a foolproof universal ID system for every human and everything else that moves. Thanks to massive breaches at Yahoo! and Equifax, the current ID system has completely failed, prompting renewed calls for a universal ID system.