|
Getting your Trinity Audio player ready... |
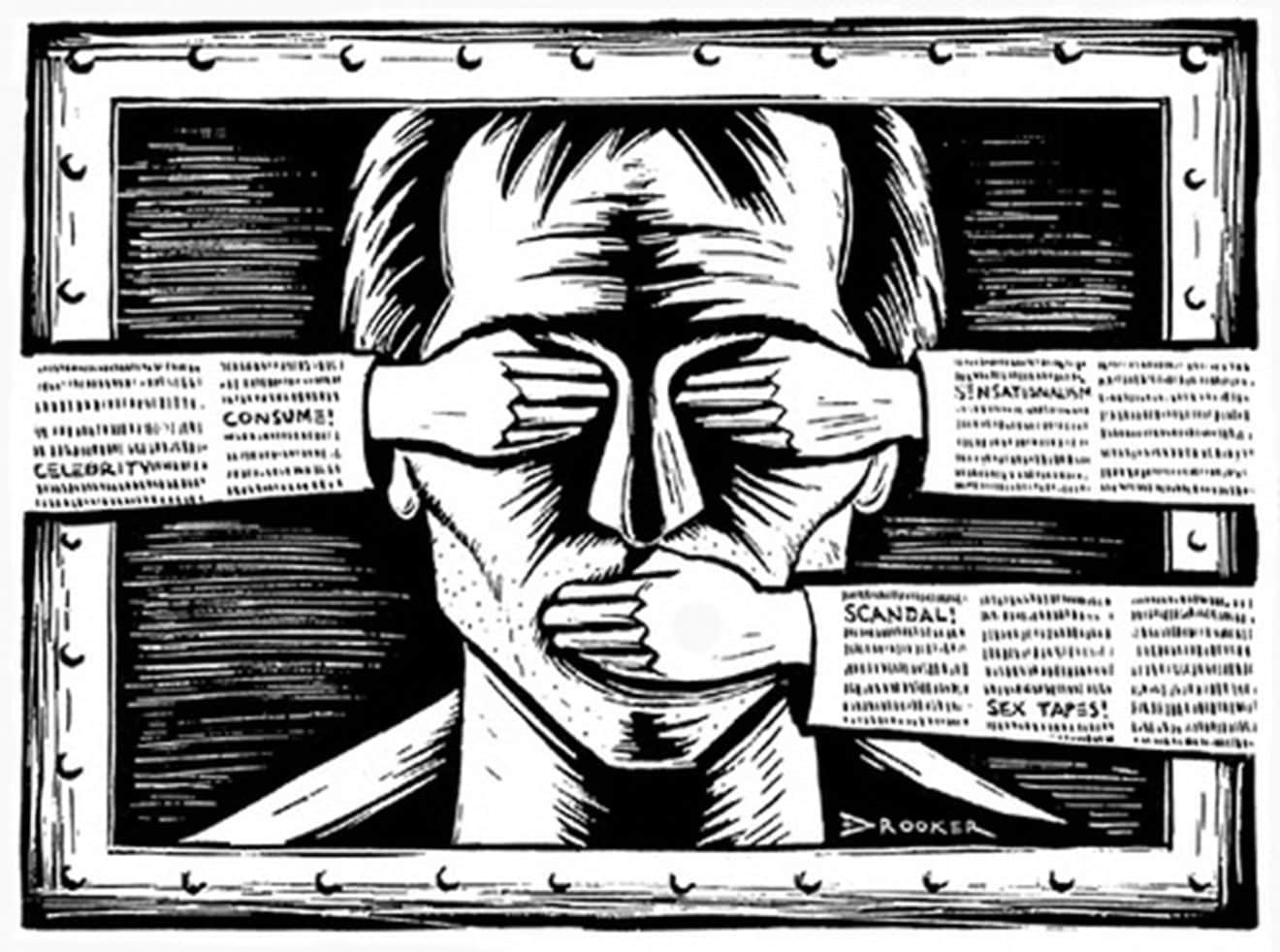
Download this post... The US Department of Defense (DoD) wants contractors to mine your social media posts to develop new ways for the US government to infer what you’re really thinking and feeling — and to predict what you’ll do next. Pentagon documents released over the last few months identify ongoing classified research in this area that...