|
Getting your Trinity Audio player ready... |
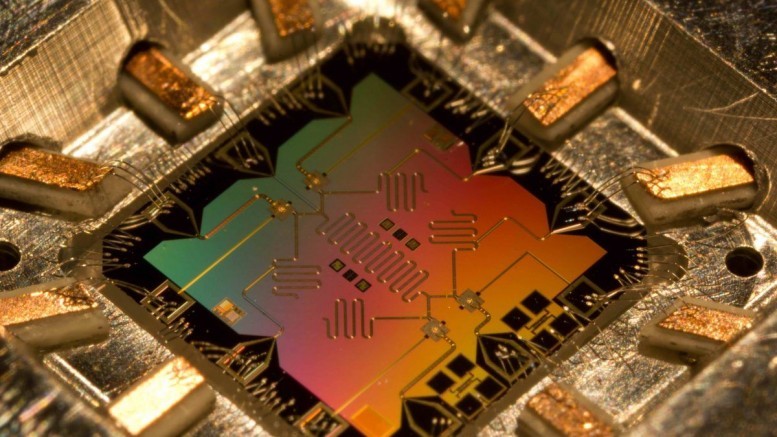
The usefulness of quantum computers is a hotly debated topic, from those who think it is quackery to others who say it's the future of computing. Regardless, scientists are pouring billions of research dollars into proving commercial uses, such as a hack-proof quantum Internet.